By now, many non-IT and non-Security folk have heard of Firesheep, a tool written by @codebutler which allows anyone using Firefox on unprotected networks to capture and hjijack active sessions to popular social media sites (and other web sites). The sidebar/extension puts an attactive and easy-to-understand GUI over a process that “real” security people have been using for as long as there has been http-based sessions.
I’ve been using Firesheep quite a bit in non-echo-chamber demos to help illustrate some of the core issues facing enterprises and individual users. A big question that comes out of each demo is “what can I do to safeguard my access to Facebook?”. I provide quick guidance on-the-spot to interested individuals and wanted to share what I communicate to them here both to help a broader audience and get feedback on other steps users can take to safeguard their connections.
General Guidance
The first action I tell users to take is an anti-action: if at all possible, never use free/unsecured Wi-Fi connections. While there are ways of grabbing sessions and other data on wired or secure Wi-Fi networks, the means to do so are beyond the capabilities of most Firesheep users. The danger is still present and you should always consider how much you trust the network you are on when accessing anything on the Internet, but the risk is greatly diminished.
If users are unable or unwilling to follow that first action (and even if they do avoid insecure networks) I then instruct them to ensure that all services they access always use “https“ (SSL/TLS) which encrypts the communication and prevents tools like Firesheep from working. It still – much like the first action – doesn’t stop determined & skilled attackers.
I then caution users on smartphones and tablets to also make sure any applications they use also communicate over SSL. This is far too easy to overlook and can leak data just as easily as a web browser. Tablet & smartphone users can also switch to only using 3G connections to make it that much more difficut for otherrs to eavesdrop.
Finally, I suggest using a virtual private networking (VPN) service such as PureVPN to secure all their connections – not just browser sessions – on public networks (secured or otherwise). SSL/TLS connections are potentially susceptible to what is called a man-in-the-middle (MITM) attack [SANS Reading Room (PDF)] and one way to mitigate that threat is to use a VPN to secure all network communication using a more robust/holistic solution. PureVPN (and other, similar good services) are not free, but $5.00-10.00USD per month is not much to pay for personal data security on-the-go.
The Elephant In The Room
![]() For some reason, even with that general guidance, the whole concept of someone hijacking their Facebook account really scares folks and many end up asking specific question on ensuring their Facebook access is protected. This usually involves walking them through how to check to see if SSL is enabled by Facebook’s service and also how to monitor access to their Facebook account.
For some reason, even with that general guidance, the whole concept of someone hijacking their Facebook account really scares folks and many end up asking specific question on ensuring their Facebook access is protected. This usually involves walking them through how to check to see if SSL is enabled by Facebook’s service and also how to monitor access to their Facebook account.
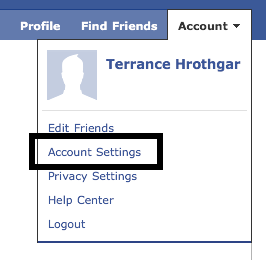
Unsurprisingly, Facebook does not make setting SSL as a default an easy task. It’s unintuitively not under any “privacy” settings. Instead, you need to navigate down to account settings and poke around to get to the right areas. The screen captures below show the navigation sequence. You’ll notice that this account does not have security enabled since it’s the one I use for demos (I do not have a personal Facebook account).
You’ll also notice that you can have Facebook send you an e-mail when there is an access to your account from an unknown device and also review recent activity on your account. This gives you the ability to be in control as much or as little as you desire.
Homeward Bound
I usually close with guidance on securing your home Wi-Fi network. Many users still have an aging 802.11b/g router that barely does wired-equivalent-privacy (WEP) security. Even newer Wi-Fi equipment with Wi-Fi Protected Access (WPA/WPA2) may not be enough as you or someone else in your house most likely handout the access password to any guest you allow in the residence. Any malware on their systems now has the potential to infect other systems on your network and you have also given the keys to your local security to someone you may not fully trust. Many of the newest Wi-Fi access points – such as Apple AirPort Extremes and Netgear N[3|6]00s – provide for the ability to setup both a protected internal network and as open of a guest network as you want. I still suggest ensuring that the guest network be secured as you may be liable for any actions taken from your network (protected or otherwise).
Highway Safety
Being safe[r] on the Internet is much lke being safe[r] when driving a car. You need to make sure the fluids are at the right levels, that the tire pressure is sufficient for the driving conditions and that you wear your seatbelt before leaving the driveway. If you don’t regularly perform those tasks you run the risk of significant problems out on the road. You need to get in the habit of doing similar checks when navigating in potentially dangerous network territory as well. It doesn’t help that Facebook cares not a whit about your privacy or security and will seemingly randomly change your settings if it benefits them (or if they are just their usual incompetent selves). Want proof? You have to be diligent in the maintenance of all Internet security settings to ensure your consistent, personal online safety.